TLS Encrypted
Table of Contents
Quicklinks: Wireshark Equivalent
You must have tshark 2.4.0 or higher to use the --export-files flag.
You must have tshark 2.6.3 or higher to decrypt TLS1.3.
About
It is possible to decrypt the data on the client side if SSL logging is enabled. Chrome and firefox will check whether the $SSLKEYLOGFILE environmental variable exists, and if it does, will send keys to the file. Using tshark and firefox, we will be able to extract the html file.
ss64.com uses TLS1.2, but the process is the same for TLS1.3.
Example: TLSv2 and ss64.com
1. Add the SSLKEYLOGFILE environment variable
Linux/Macos
If you only want to use the sslkeylogfile in this session, use export.
export SSLKEYLOGFILE=/tmp/sslkey.log
To use the same file permanently (in bash), you can add it to your ~/.bashrc.
echo "export SSLKEYLOGFILE=/tmp/sslkey.log" >> ~/.bashrc
source ~/.bashrc
Verification
Check that the variable is available.
bash$ echo $SSLKEYLOGFILE
/tmp/sslkey.log
Windows
To set the variable for your system, use SetX.
# Sets the HKCU\Environment User Environment variable
PS C:\Users\rj\Desktop> SetX SSLKEYLOGFILE "$(get-location)\ssl.log"
SUCCESS: Specified value was saved.
Verification
SetX does not apply to the current session.
To verify, check SSLKEYLOGFILE in a new powershell window:
PS C:\Users\rj\Desktop> Get-ChildItem ENV: | findstr SSLKEYLOGFILE
SSLKEYLOGFILE C:\Users\rj\desktop\ssl.log
2. Capture traffic going to a website
Let’s use ss64.com as it is designed to be
lightweight. They have an article on netcat (nc), which seems apropos to use: https://ss64.com/bash/nc.html.
In this example, we will be capturing for 10 seconds with tshark while saving the HTML with firefox.
We are using firefox because captures containing its usage have predictable file names. curl and wget by comparison have captures that contain
a multitude of files like “object1234” and “object2345” when exported as files from tshark.
cd /tmp
url='https://ss64.com/bash/nc.html'
# -a to wait 10 sec, -Q for suppress output
tshark -Q -a duration:5 -w /tmp/myfile.pcapng &
# Wait 5 seconds for firefox to access content and then kill
firefox --headless --private $url & ffpid=$!
sleep 5 && kill -9 $ffpid
3. Export http objects to obj/
mkdir -p /tmp/obj
# Equivalent to Wireshark > File > Export Objects > HTTP
tshark -Q --export-objects http,/tmp/obj -r /tmp/myfile.pcapng \
-o tls.keylog_file:$SSLKEYLOGFILE
4. Verify that HTML extraction was successful
The two relevant files that we receive from ss64.com are nc.html and
main.css. This HTML file references its css file as “../main.css”, so
create a symbolic link for verification purposes and then open it.
ln -s obj/main.css main.css
firefox --browser obj/nc.html
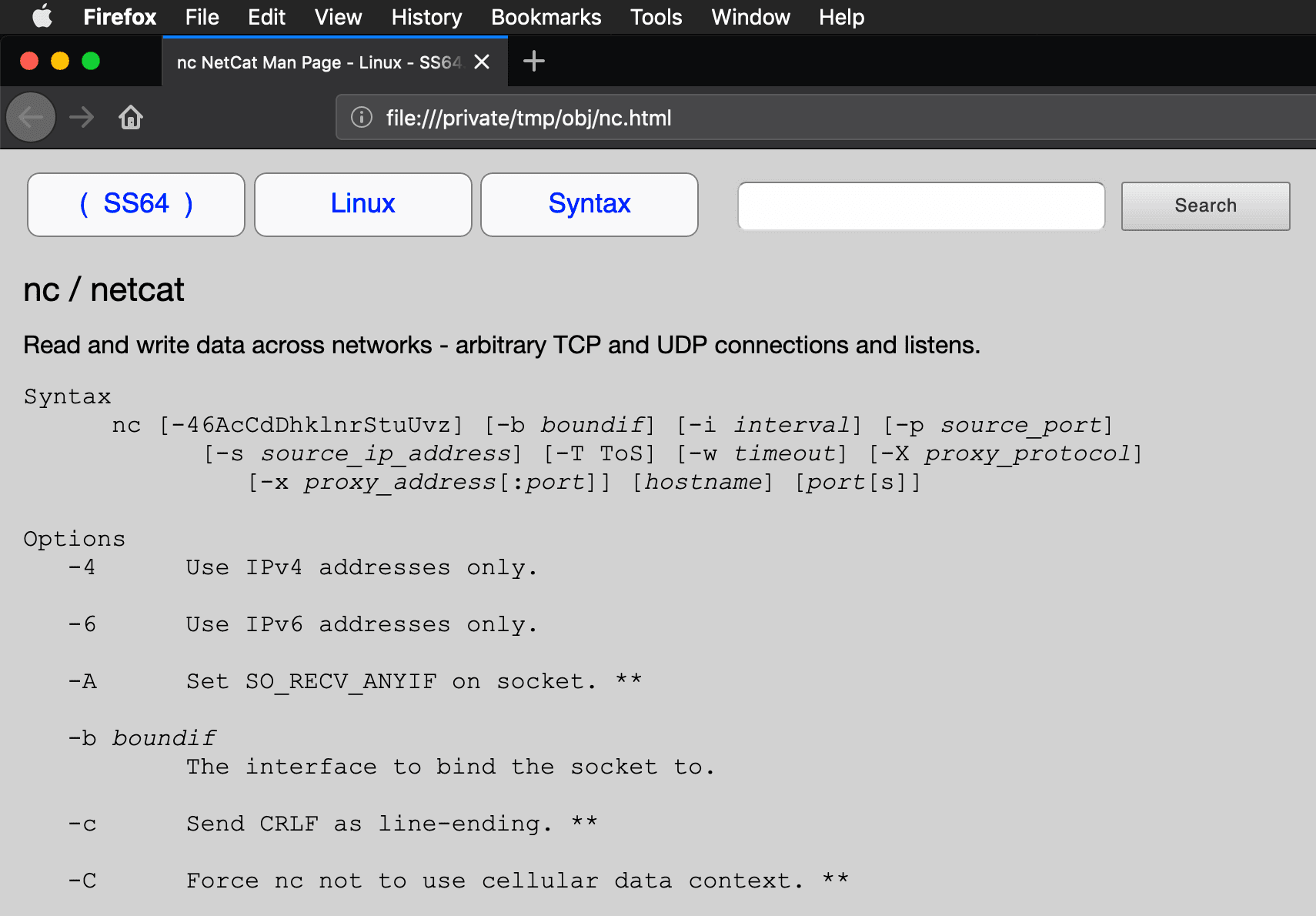
If all is well, your local version of nc’s manpage looks like this:
5. Cleaning up
Anyone that has your network traffic AND your SSLKEYLOGFILE can decrypt it. For the security conscious, unset this variable once you are done.
Linux/Macos
unset $SSLKEYLOGFILE
Windows
Be careful when you work with the registry, as it is easy to shoot yourself in the foot when making a change.
Assuming you set without the /M flag for the User Environment:
REG delete HKCU\Environment /F /V SSLKEYLOGFILE
Asciicast of This Example
Further Reading
- 2018-12-07, F5, Decrypting SSL traffic with the SSLKEYLOGFILE environment variable
- 2013-08-07, Steven Iveson, Using Wireshark to Decode SSL/TLS Packets